Application Packaging in a Nutshell: Introduction to Basics
Software application packaging is about managing apps across your organization or end users. Its primary goal is to help ensure all users have an up-to-date version of the app, which runs smoothly on their devices. No matter what platform or device they are using.
Whether you’re just starting your journey in the world of software packaging, looking for a way to simplify your team’s daily routine, or considering changing the app packaging tool, you’re in the right place. We’ll guide you from the basics to the challenges you may overcome, using the right solution.
Let’s get straight to the point: what is software packaging? If you’re already familiar with it, skip to the next section.
What is Application Packaging? Plus Some Other Definitions
Application packaging (or software packaging) means wrapping up all app resources in one file and distributing it to your users. They can launch this file to set up and/or update your app on their devices.
This file (or package) contains all components necessary to install and run the app. In fact, this is the installer.
Here’s a short glossary for other app packaging-related terms and abbreviations you may come across:
- Build means a version of the app ready for testing or use. To create a build, developers compile source code into a fully-functional application. The latter can launch and work across devices.
- Compilation is a process of transforming readable source code into binary machine code.
- Deployment is about delivering apps, patches, modules, or updates to end users.
- Microsoft SCCM stands for Microsoft System Center Configuration Manager. This tool helps to manage and distribute apps across enterprises. It also ensures the IT infrastructure is protected from malware.
- Patches are the changes related to application software updates or fixes (e.g., eliminating security vulnerabilities).
- Registry keys are containers (think of them as folders) with registry subkeys that hold registry values. Their primary function is to record and store different Windows configurations (for instance, info about computer users, software installed, time and language settings, etc.).
- Repo (repository) is the main storage of software files and packages.
Now that you know what app packaging is, it’s time to dive deeper into the nuances of packaging basics.
Software Packaging Essentials: Formats, Methods, Processes
Let’s focus on other things you may need to know: types of packages, packaging methods, processes, and repackaging specifics.
As far as Windows holds 75.93% of the OS market share, Microsoft installers prevail. Here are the most widespread package formats:
- EXE (executable file) is an outdated application installer, yet many companies still use it. The apps in this format are hard to customize and don’t support silent installation.
- MSI is an app installer for Windows OS. You can also use it for the deployment of patches and updates.
- MSIX is the latest Microsoft app package installer version, launched with the Windows 10 release.
- App-V is designed to run apps virtually, so you don’t have to install them on your device.
Need more details about the most popular app packaging formats? Check out our article The Most Popular Application Packaging Formats And Their Characteristics.
Basic Software Packaging Methods
There are two general packaging methods: virtual and non-virtual. To differentiate them, you need to define whether the app is installed directly on the device or runs virtually.
Non-virtual packages are the most common ones. Windows Installer (MSI) is an example of a non-virtual package.
To run the app, you should install such a package “physically” to your operating system. The installed app will use some storage and interact with system files, registry keys, and environment variables.
Virtual packages imitate all those resources, including file and security systems. In other words, these packages virtualize applications, so that the latter can run on the device without being installed on it. Thus, you can reduce the risks of possible OS crashes because of app installation.
How Does the Packaging Process Look?
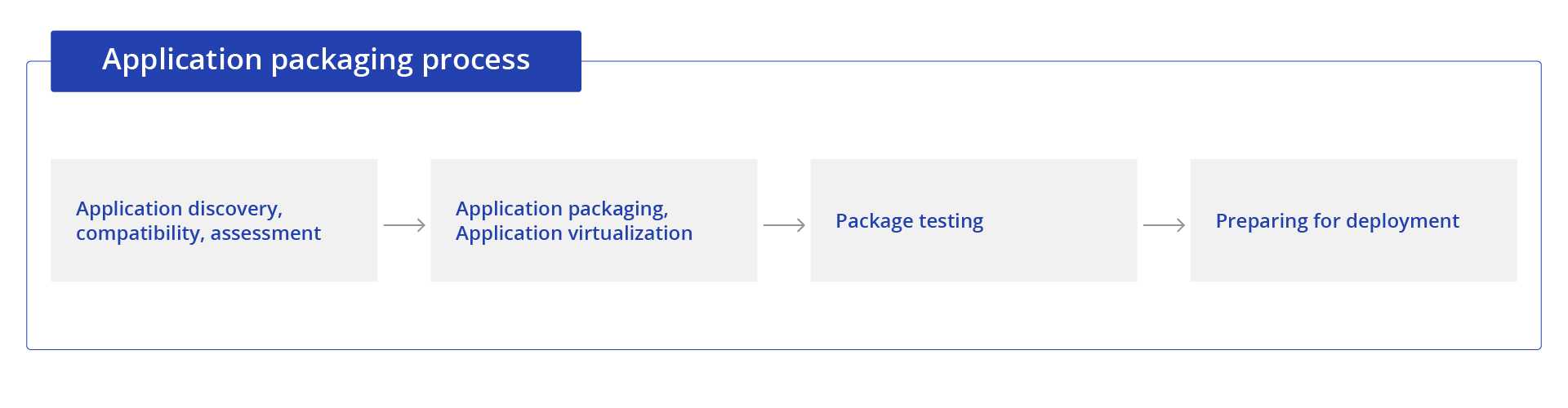
App packaging itself is a part of the larger process that starts with the need for app launch or scaling and ends with the actual delivery of the application to the end users. The whole process looks as follows:
Step-by-step packaging process
- Application discovery: Check the source file and validate its compatibility with your organization’s environment, record app details, configs, use cases, and any other outputs, essential for packaging.
- App packaging: Package the app according to the requirements collected and create a build, ready for review.
- Testing: This stage is intended to check app functionality and make sure all requirements are met, so the app works as it should. In case any issues are discovered, this step is also for fixing them and rolling out the new build.
- Application delivery: After the testing in the staging environment, prepare application for deployment to production and further distribution to your users.
Another important thing that isn’t in this flow but should be a regular process is applications rationalization. This means you should systematically audit the apps utilized in your organization to decide what to do next—update, fix, remove, or repackage them.
What Is Application Packaging and Repackaging?
So, what is application software repackaging? To put it simply, it’s creating a new installer package after changing the original files.
The procedure may come in handy when you need to standardize your apps or upgrade them (e.g., from EXE to MSI). Yet, it’s better not to repackage your application if its source installer comes with an embedded MSI, as this may cause crashes or even functionality loss. To avoid that, we recommend opting for MSI transform.
Sure, you can do this manually, but usually, it takes a lot of time for development and testing. Just compare:
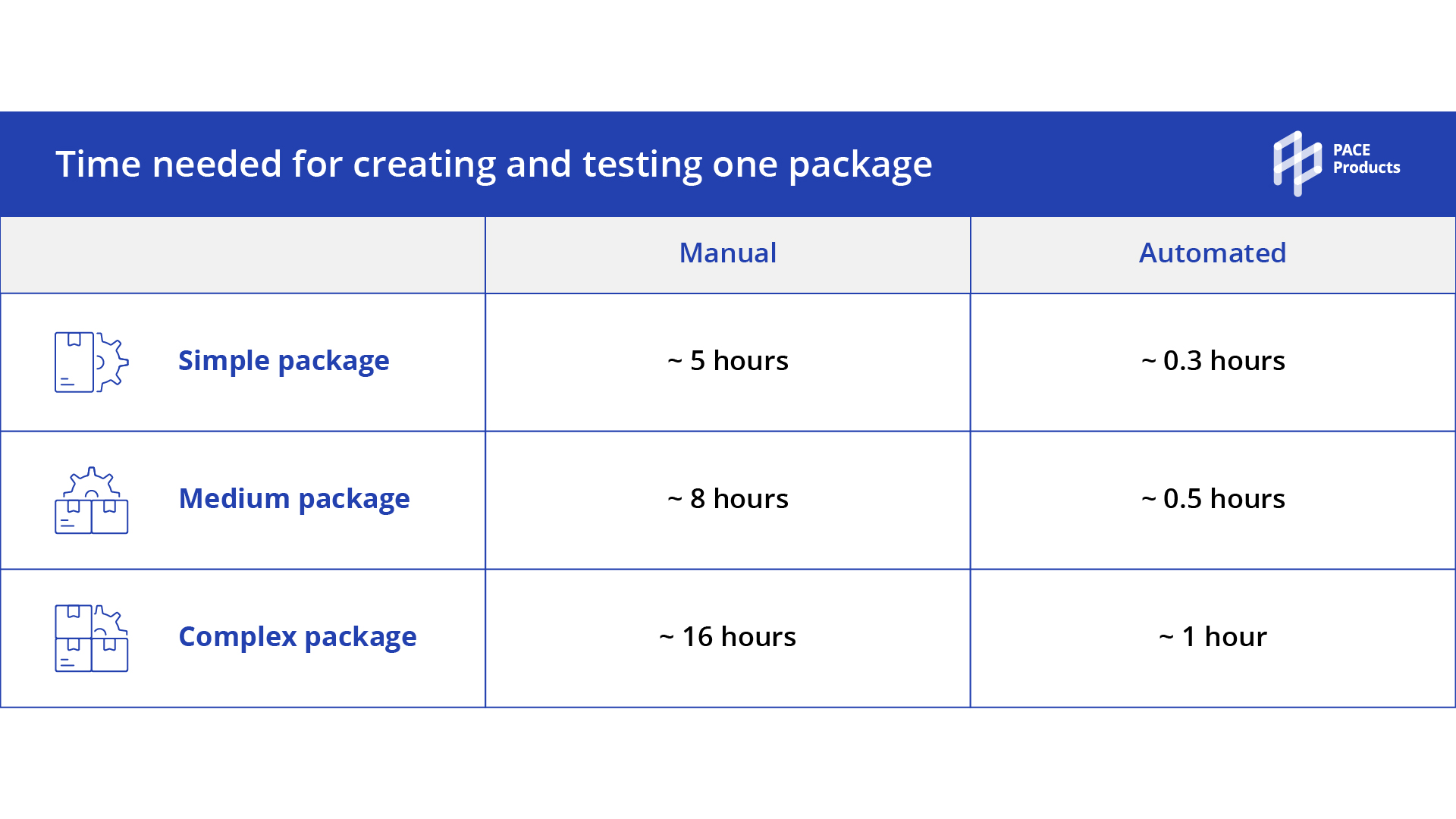
Why waste it if you can use ready-made solutions to automate such routine operations?
Let’s move on to what other issues with app packaging you can address by using relevant tools.
What Challenges Do App Packaging Tools Help to Overcome?
We’ll cover the advantages of software packaging in our next articles. For now, let’s briefly review the main challenges you can solve by using app packaging tools.
- Slow package delivery. As we’ve already mentioned, with specialized solutions, you can reduce the time spent on packaging, testing, and distribution up to 15 hours.
- Difficult customization or packaging format change. It requires lots of manual configurations. As a result, you spend more resources on it.
- Keeping your infrastructure up-to-date. Checking and upgrading each app on each device sounds like an impossible mission. With automated application packaging solutions, you can achieve an evergreen IT with stable and standardized processes.
- Impossibility to make fast changes to vendor installations. Software packaging tools empower build engineers to quickly update installers and create transforms.
Find more possible solutions to your challenges in our applications packaging software trends overview.
Who and Why May Need Application Packaging?
Depending on your business size, you can pursue different goals of app packaging.
Individual app product owners might need to quickly publish updates or fixes to the repositories. They can also need to repackage applications, especially if the previous installer file format is no longer supported.
Huge enterprises might need quick application wrapping and delivery to multiple users across the company network. Especially, if an organization has offices and employees in different countries and locations. Also, if an enterprise uses dozens of apps, it can look for automating app packaging.
To sum it up
We hope that now you’ve got a picture of what software packaging is and how to adopt it with minimum pain. So, let’s rewind the reasons you may need to opt for an app packaging tool:
- Wrapping up legacy setup files so that they could launch in your target environment
- Changing installers’ format by repackaging (for instance, from EXE to MSI)
- Introducing changes to an MSI file through MST
- Virtualizing applications to minimize their influence on corporate infrastructure
- Saving time and resources on app upgrades and distribution
- Ensuring apps comply with company security and user policies
- Keeping evergreen IT and others
Want to try an out-of-the-box solution that matches your needs?
We have one and will gladly navigate you through all details.